Meet us at CES2018 in Las Vegas

Back to news TrustInSoft at the Business France Automotive Pavilion, stand CP-5, Central Plaza, at CES, on January 9-12, 2018 CES2018 – Las Vegas From tech powerhouses to innovative startups, companies big and small from all industries come to CES to introduce the latest innovation to the global market. It has served as the proving […]
Come meet us at ESC SILICON VALLEY 2017

icon/arrow Back to news See you at ESC Silicon Valley, December 5-7, 2017! TrustInSoft at ESC Silicon Valley 2017 TrustInSoft is attending Silicon Valley’s Premier Embedded Systems Showcase on December 5-7, 2017, at the San Jose Convention Center. ESC Silicon Valley provides access to a comprehensive showcase of industry suppliers and technical education, including presentations, demos, […]
Our 1st Free & Online Source Code Analyzer launched at Arm TechCon
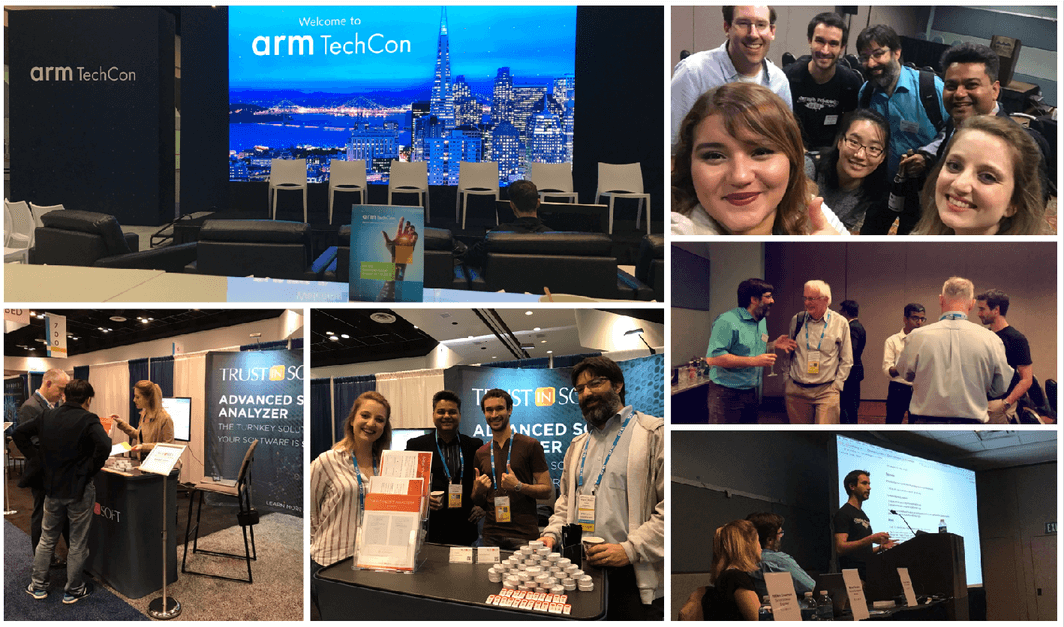
Back to news Product launch at ARM TechCon. Online Source Code Analyzer Launch TrustInSoft attended ARM TechCon last week from the 24th to the 26th of October in Santa Clara, CA. It was a great show, and our booth was very busy. We also hosted our product launch party on Wednesday 25th. We enjoyed a […]
TrustInSoft at ISSA Conference & SDN NFV World Congress
Back to news Learn about our commitment to safety and cybersecurity by visiting us at either of these conferences Join TrustInSoft at ISSA Conference and NFV World Congress It is important for us to have a presence in all the events that are related to our fields of knowledge and expertise: Safety & Cybersecurity. This week, TrustInSoft is attending […]
Come see us at World e-ID & CyberSecurity 2017

Back to news Meet TrustInSoft at the 13th edition of World e-ID & CyberSecurity for Smart Security Week TrustInSoft at World e-ID & CyberSecurity 2017 TrustInSoft is attending the 13th edition of World e-ID and Cybersecurity congress at palais Pharo, an exceptional setting . This year’s edition explores the latest secure identification technologies, their […]
Nato and the Future of Cybersecurity

Back to news Jamie Shea and TrustInSoft CEO Fabrice Derepas discuss formal methods Evolution of Cybersecurity and NATO Cybersecurity is a quickly developing industry. NATO’s objective is to detect emerging cybersecurity challenges. Jamie Shea, Deputy Assistant Secretary General for Emerging Security Challenges at NATO is tasked with this monumental undertaking. In the above picture […]
Come See TrustInSoft at ARM TechCon

Back to news Visit TrustInSoft at booth 732 to discuss software security TrustInSoft at ARM TechCon in October TrustInSoft is attending the world’s biggest ARM event, ARM TechCon October 25-27 at the Santa Clara Convention Center. The conference brings together top tier suppliers who are able to meet specific embedded needs. We will be showcasing our […]
Bulletproof software for cars

Back to news TrustInSoft in San Francisco at Automotive Cybersecurity Summit Join TrustInSoft at Automotive Cyber Security Summit You want to build bulletproof software for your car? Come and meet TrustInSoft at Automotive Cybersecurity Summit on October 6 and 7 in Hotel Kabuki. You’ll discover how formal methods can help you secure the most […]
Pitching with Axelle Lemaire

Back to news Pitching about software safety and security for connected cars to Axelle Lemaire, Minister of State in charge of Digital Affairs. Twitter link Newsletter Related articles See more news
Fast & Serious

Back to news TrustInSoft takes home the prize at the 6WIND Speed Matters contest TrustInSoft won the “Grand Prize” during the 6WIND “Speed Matters” contest. So we got the nice 50mph green car on the picture! We already knew the power of 6WIND software, that can unleash the speed of multicore processors to create […]